
Protect your digital assets with confidence.
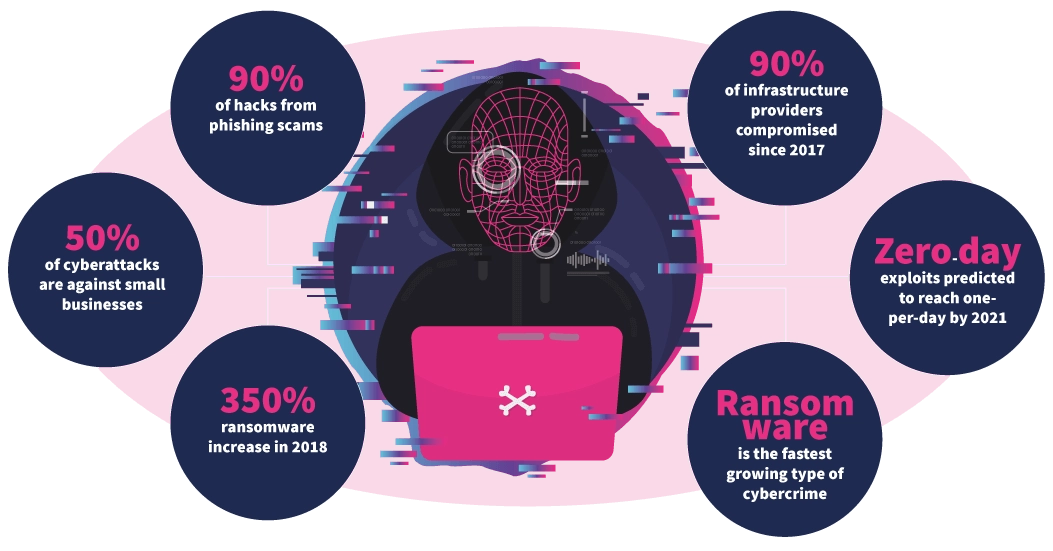
With cyber threats evolving daily, robust protection is essential. I offer a comprehensive range of cybersecurity services designed to detect vulnerabilities, mitigate risks, and fortify your digital infrastructure.
Specialized Services
Cybersecurity Services
Risk Assessment & Management
Vulnerability Assessment & Penetration Testing (VAPT):
Identify and remediate security weaknesses in your systems, networks, and applications before attackers exploit them.
Cybersecurity Risk Management:
Evaluate threats, define security controls, and ensure continuous monitoring to enhance resilience against cyber threats.Security Audits & Compliance:
Conduct audits aligned with global standards like ISO/IEC 27001 to ensure adherence to regulatory and industry-specific security requirements.
Incident Response & Recovery

Incident Response Planning:
Prepare your organization for cyber incidents with tested plans, training, and expert guidance to minimize impact and facilitate swift recovery.Digital Forensics & Investigation:
Investigate breaches, trace attacker footprints, and recover digital evidence for internal analysis or legal action.Ransomware Protection & Recovery:
Develop strategies to defend against ransomware attacks and establish recovery protocols to minimize downtime and data loss.
Security Operations & Monitoring
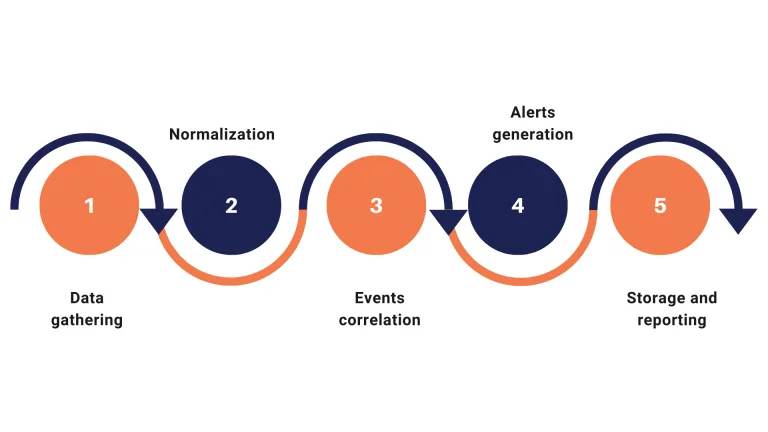
Security Information and Event Management (SIEM):
Collect and analyze security data across your organization to detect, analyze, and respond to security incidents in real-time.Endpoint Detection and Response (EDR):
Monitor and respond to threats on endpoint devices to prevent data breaches and malware infections.Managed Detection and Response (MDR):
Provide outsourced monitoring and management of security systems to detect, analyze, and respond to threats effectively.
Identity & Access Management
Identity and Access Management (IAM):
Ensure that the right individuals access the appropriate resources at the right times for the right reasons, enhancing security and compliance.Multi-Factor Authentication (MFA):
Implement additional layers of authentication to strengthen access controls and reduce the risk of unauthorized access.Privileged Access Management (PAM):
Control and monitor access to critical systems by privileged users to prevent unauthorized activities.
Data Protection & Privacy

Data Loss Prevention (DLP):
Implement policies and tools to prevent unauthorized access, transfer, or destruction of sensitive data, safeguarding against data breaches.Data Encryption Services:
Apply encryption protocols to protect sensitive data both at rest and in transit.Privacy Impact Assessments (PIA):
Evaluate the impact of projects on data privacy and ensure compliance with regulations.
Cloud & Application Security

Cloud Security Services:
Secure cloud-based infrastructures, applications, and data through assessments, compliance checks, and tailored security strategies.Application Security Testing:
Assess and enhance the security of your applications through code reviews, penetration testing, and implementing secure development practices.Web Application Firewall (WAF) Deployment:
Protect web applications by filtering and monitoring HTTP traffic to prevent attacks.
Security Awareness & Training

Cybersecurity Awareness Programs:
Design and facilitate engaging sessions that teach employees, students, and decision-makers how to recognize threats, protect data, and adopt cyber-safe behaviors.Phishing Simulation Campaigns:
Educate and test your team with realistic phishing scenarios to build a security-aware workplace culture.Secure Software Development Training:
Provide training on best practices for secure coding to prevent vulnerabilities from the ground up.
Compliance & Governance
Regulatory Compliance Consulting:
Assist your organization in understanding and adhering to relevant cybersecurity regulations and standards.Policy Development & Implementation:
Develop and implement comprehensive security policies tailored to your organization's needs.Third-Party Risk Management:
Assess and manage risks associated with third-party vendors and partners to protect your organization’s data and systems.

